Introduction | Safety snapshot | Menace briefing
Defending towards assaults | Professional profile
Schooling is basically an “{industry} of industries,” with Okay-12 and better training enterprises dealing with knowledge that would embody well being information, monetary knowledge, and different regulated data. On the identical time, their services can host fee processing techniques, networks which are used as web service suppliers (ISPs), and different various infrastructure. The cyberthreats that Microsoft observes throughout totally different industries are usually compounded in training, and risk actors have realized that this sector is inherently weak. With a median of two,507 cyberattack makes an attempt per week, universities are prime targets for malware, phishing, and IoT vulnerabilities.¹
Safety staffing and IT asset possession additionally have an effect on training organizations’ cyber dangers. Faculty and college techniques, like many enterprises, usually face a scarcity of IT sources and function a mixture of each trendy and legacy IT techniques. Microsoft observes that in america, college students and school are extra doubtless to make use of private units in training in comparison with Europe, for instance. No matter possession nevertheless, in these and different areas, busy customers don’t at all times have a safety mindset.
This version of Cyber Indicators delves into the cybersecurity challenges going through lecture rooms and campuses, highlighting the essential want for strong defenses and proactive measures. From private units to digital lessons and analysis saved within the cloud, the digital footprint of college districts, faculties, and universities has multiplied exponentially.
We’re all defenders.

A uniquely beneficial and weak setting
The training sector’s person base could be very totally different from a typical massive industrial enterprise. Within the Okay-12 setting, customers embody college students as younger as six years outdated. Identical to any public or non-public sector group, there’s a huge swath of workers in class districts and at universities together with administration, athletics, well being providers, janitorial, meals service professionals, and others. A number of actions, bulletins, data sources, open electronic mail techniques, and college students create a extremely fluid setting for cyberthreats.
Digital and distant studying have additionally prolonged training functions into households and places of work. Private and multiuser units are ubiquitous and sometimes unmanaged—and college students should not at all times cognizant about cybersecurity or what they permit their units to entry.
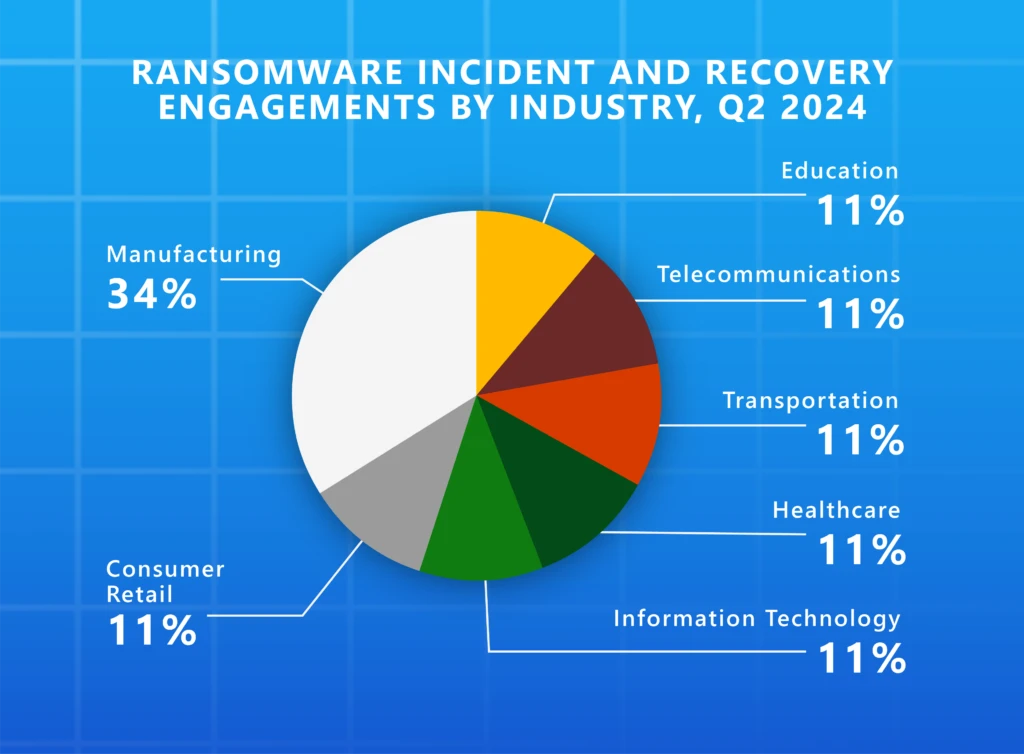
Schooling can be on the entrance traces confronting how adversaries take a look at their instruments and their strategies. In line with knowledge from Microsoft Menace Intelligence, the training sector is the third-most focused {industry}, with america seeing the best cyberthreat exercise.
Cyberthreats to training should not solely a priority in america. In line with the UK’s Division of Science Innovation and Know-how 2024 Cybersecurity Breaches Survey, 43% of upper training establishments within the UK reported experiencing a breach or cyberattack a minimum of weekly.²
QR codes present an simply disguised floor for phishing cyberattacks
At the moment, fast response (QR) codes are fairly well-liked—resulting in elevated dangers of phishing cyberattacks designed to achieve entry to techniques and knowledge. Photographs in emails, flyers providing details about campus and college occasions, parking passes, monetary assist kinds, and different official communications all steadily include QR codes. Bodily and digital training areas is perhaps essentially the most “flyer pleasant” and QR code-intensive environments anyplace, given how massive a job handouts, bodily and digital bulletin boards, and different informal correspondence assist college students navigate a mixture of curriculum, institutional, and social correspondence. This creates a beautiful backdrop for malicious actors to focus on customers who’re attempting to avoid wasting time with a fast picture scan.
Just lately america Federal Commerce Fee issued a client alert on the rising risk of malicious QR codes getting used to steal login credentials or ship malware.³
Microsoft Defender for Workplace 365 telemetry exhibits that roughly greater than 15,000 messages with malicious QR codes are focused towards the tutorial sector every day—together with phishing, spam, and malware.
Professional software program instruments can be utilized to shortly generate QR codes with embedded hyperlinks to be despatched in electronic mail or posted bodily as a part of a cyberattack. And people photos are onerous for conventional electronic mail safety options to scan, making it much more essential for college and college students to make use of units and browsers with trendy net defenses.
Focused customers within the training sector could use private units with out endpoint safety. QR codes primarily allow the risk actor to pivot to those units. QR code phishing (since its function is to focus on cellular units) is compelling proof of cellular units getting used as an assault vector into enterprises—resembling private accounts and financial institution accounts—and the necessity for cellular machine safety and visibility. Microsoft has considerably disrupted QR code phishing assaults. This shift in ways is obvious within the substantial lower in every day phishing emails intercepted by our system, dropping from 3 million in December 2023 to only 179,000 by March 2024.
Universities current their very own distinctive challenges. A lot of college tradition relies on collaboration and sharing to drive analysis and innovation. Professors, researchers, and different college function below the notion that expertise, science—merely data itself—must be shared extensively. If somebody showing as a scholar, peer, or comparable celebration reaches out, they’re usually keen to debate doubtlessly delicate subjects with out scrutinizing the supply.
College operations additionally span a number of industries. College presidents are successfully CEOs of healthcare organizations, housing suppliers, and huge monetary organizations—the {industry} of industries issue, once more. Due to this fact, prime leaders can could be prime targets for anybody attacking these sectors.
The mixture of worth and vulnerability present in training techniques has attracted the eye of a spectrum of cyberattackers—from malware criminals using new strategies to nation-state risk actors participating in old-school spy craft.
Microsoft regularly screens risk actors and risk vectors worldwide. Listed here are some key points we’re seeing for training techniques.
E mail techniques in colleges provide huge areas for compromise
The naturally open setting at most universities forces them to be extra relaxed of their electronic mail hygiene. They’ve loads of emails amounting to noise within the system, however are sometimes operationally restricted in the place and the way they will place controls, due to how open they should be for alumni, donors, exterior person collaboration, and lots of different use circumstances.
Schooling establishments are likely to share loads of bulletins in electronic mail. They share informational diagrams round native occasions and college sources. They generally permit exterior mailers from mass mailing techniques to share into their environments. This mix of openness and lack of controls creates a fertile floor for cyberattacks.
AI is rising the premium on visibility and management
Cyberattackers recognizing increased training’s give attention to constructing and sharing can survey all seen entry factors, searching for entry into AI-enabled techniques or privileged data on how these techniques function. If on-premises and cloud-based foundations of AI techniques and knowledge should not secured with correct id and entry controls, AI techniques grow to be weak. Simply as training establishments tailored to cloud providers, cellular units and hybrid studying—which launched new waves of identities and privileges to control, units to handle, and networks to phase—they have to additionally adapt to the cyber dangers of AI by scaling these timeless visibility and management imperatives.
Nation-state actors are after beneficial IP and high-level connections
Universities dealing with federally funded analysis, or working intently with protection, expertise, and different {industry} companions within the non-public sector, have lengthy acknowledged the chance of espionage. Many years in the past, universities centered on telltale bodily indicators of spying. They knew to search for folks displaying up on campus taking photos or attempting to get entry to laboratories. These are nonetheless dangers, however right this moment the dynamics of digital id and social engineering have vastly expanded the spy craft toolkit.
Universities are sometimes epicenters of extremely delicate mental property. They might be conducting breakthrough analysis. They might be engaged on high-value tasks in aerospace, engineering, nuclear science, or different delicate subjects in partnership with a number of authorities businesses.
For cyberattackers, it may be simpler to first compromise someone within the training sector who has ties to the protection sector after which use that entry to extra convincingly phish a better worth goal.
Universities even have specialists in overseas coverage, science, expertise, and different beneficial disciplines, who could willingly provide intelligence, if deceived in social-engineering cyberattacks using false or stolen identities of friends and others who look like in people’ networks or amongst trusted contacts. Other than holding beneficial intelligence themselves, compromised accounts of college workers can grow to be springboards into additional campaigns towards wider authorities and {industry} targets.
Nation-state actors focusing on training

Peach Sandstorm has used password spray assaults towards the training sector to achieve entry to infrastructure utilized in these industries, and Microsoft has additionally noticed the group utilizing social engineering towards targets in increased training.
Microsoft has noticed a subset of this Iranian assault group focusing on high-profile specialists engaged on Center Japanese affairs at universities and analysis organizations. These subtle phishing assaults used social engineering to compel targets to obtain malicious recordsdata together with a brand new, customized backdoor referred to as MediaPl.
Mabna Institute
In 2023, the Iranian Mabna Institute carried out intrusions into the computing techniques of a minimum of 144 United States universities and 176 universities in 21 different international locations.
The stolen login credentials had been used for the good thing about Iran’s Islamic Revolutionary Guard Corps and had been additionally offered inside Iran by means of the online. Stolen credentials belonging to school professors had been used to instantly entry college library techniques.

This North Korean group primarily targets specialists in East Asian coverage or North and South Korean relations. In some circumstances, the identical teachers have been focused by Emerald Sleet for almost a decade.
Emerald Sleet makes use of AI to write down malicious scripts and content material for social engineering, however these assaults aren’t at all times about delivering malware. There’s additionally an evolving pattern the place they merely ask specialists for coverage perception that might be used to control negotiations, commerce agreements, or sanctions.
Moonstone Sleet is one other North Korean actor that has been taking novel approaches like creating faux corporations to forge enterprise relationships with instructional establishments or a specific college member or scholar.
Probably the most outstanding assaults from Moonstone Sleet concerned making a faux tank-themed recreation used to focus on people at instructional establishments, with a purpose to deploy malware and exfiltrate knowledge.

Storm-1877
This actor largely engages in cryptocurrency theft utilizing a customized malware household that they deploy by means of varied means. The final word purpose of this malware is to steal crypto pockets addresses and login credentials for crypto platforms.
College students are sometimes the goal for these assaults, which largely begin on social media. Storm-1877 targets college students as a result of they might not be as conscious of digital threats as professionals in {industry}.
A brand new safety curriculum
As a consequence of training finances and expertise constraints and the inherent openness of its setting, fixing training safety is greater than a expertise drawback. Safety posture administration and prioritizing safety measures is usually a expensive and difficult endeavor for these establishments—however there’s a lot that college techniques can do to guard themselves.
Sustaining and scaling core cyberhygiene will probably be key to securing faculty techniques. Constructing consciousness of safety dangers and good practices in any respect ranges—college students, college, directors, IT workers, campus workers, and extra—may help create a safer setting.
For IT and safety professionals within the training sector, doing the fundamentals and hardening the general safety posture is an effective first step. From there, centralizing the expertise stack may help facilitate higher monitoring of logging and exercise to achieve a clearer image into the general safety posture and any vulnerabilities.
Oregon State College
Oregon State College (OSU), an R1 research-focused college, locations a excessive precedence on safeguarding its analysis to keep up its popularity. In 2021, it skilled an in depth cybersecurity incident not like something earlier than. The cyberattack revealed gaps in OSU’s safety operations.
“The varieties of threats that we’re seeing, the varieties of occasions which are occurring in increased training, are far more aggressive by cyber adversaries.”
—David McMorries, Chief Data Safety Officer at Oregon State College
In response to this incident, OSU created its Safety Operations Heart (SOC), which has grow to be the centerpiece of the college’s safety effort. AI has additionally helped automate capabilities and helped its analysts, who’re faculty college students, learn to shortly write code—resembling risk looking with extra superior looking queries.
Arizona Division of Schooling
A give attention to Zero Belief and closed techniques is an space that the Arizona Division of Schooling (ADE) takes additional than the state necessities. It blocks all visitors from outdoors america from its Microsoft 365 setting, Azure, and its native datacenter.
“I don’t permit something uncovered to the web on my decrease dev environments, and even with the manufacturing environments, we take further care to guarantee that we use a community safety group to guard the app providers.”
—Chris Henry, Infrastructure Supervisor on the Arizona Division of Schooling
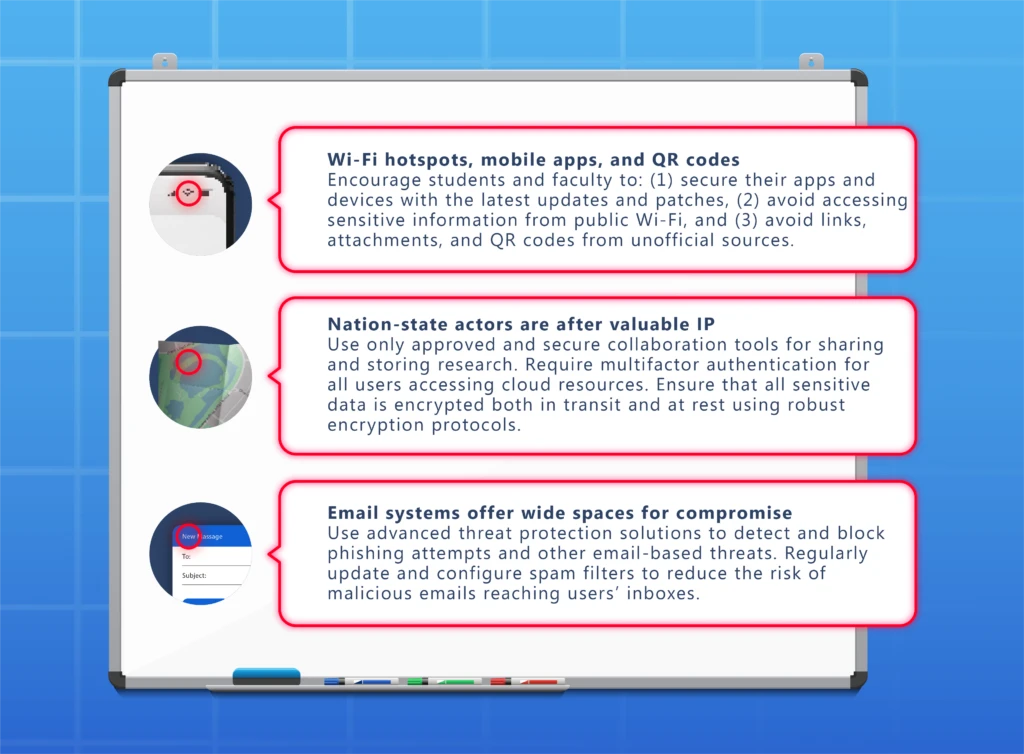
Comply with these suggestions:
- The very best protection towards QR code assaults is to remember and concentrate. Pause, examine the code’s URL earlier than opening it, and don’t open QR codes from surprising sources, particularly if the message makes use of pressing language or comprises errors.
- Take into account implementing “protecting area identify service,” a free device that helps stop ransomware and different cyberattacks by blocking pc techniques from connecting to dangerous web sites. Stop password spray assaults with a stringent password and deploy multifactor authentication.
- Educate college students and workers about their safety hygiene, and encourage them to make use of multifactor authentication or passwordless protections. Research have proven that an account is greater than 99.9% much less prone to be compromised when utilizing multifactor authentication.

Corey Lee has at all times had an curiosity in fixing puzzles and crimes. He began his faculty profession at Penn State College in legal justice, however quickly realized his ardour for digital forensics after taking a course about investigating a desktop pc break-in.
After finishing his diploma in safety and threat evaluation, Corey got here to Microsoft centered on gaining cross-industry expertise. He’s labored on securing every little thing from federal, state, and native businesses to industrial enterprises, however right this moment he focuses on the training sector.

After spending time working throughout industries, Corey sees training by means of a unique lens—the considerably distinctive {industry} of industries. The dynamics at play contained in the training sector embody tutorial establishments, monetary providers, essential infrastructure like hospitals and transportation, and partnerships with authorities businesses. In line with Corey, working in such a broad discipline permits him to leverage skillsets from a number of industries to handle particular issues throughout the panorama.
The truth that training may be referred to as underserved from a cybersecurity standpoint is one other compelling problem, and a part of Corey’s private mission. The training {industry} wants cybersecurity specialists to raise the precedence of defending faculty techniques. Corey works throughout the general public and {industry} dialogue, skilling and readiness applications, incident response, and total protection to guard not simply the infrastructure of training, however college students, dad and mom, lecturers, and workers.
At the moment, Corey is targeted reimagining scholar safety operations facilities, together with inject AI into the equation and convey trendy expertise and coaching to the desk. By rising the cybersecurity work drive in training and giving them new instruments, he’s working to raise safety within the sector in a method that’s commensurate with how essential the {industry} is for the longer term.
Subsequent steps with Microsoft Safety
To be taught extra about Microsoft Safety options, go to our web site. Bookmark the Safety weblog to maintain up with our professional protection on safety issues. Additionally, observe us on LinkedIn (Microsoft Safety) and X (@MSFTSecurity) for the newest information and updates on cybersecurity.
¹World Cyberattacks Proceed to Rise with Africa and APAC Struggling Most, Test Level Weblog. April 27, 2023.
²Cyber safety breaches survey 2024: training establishments annex, The UK Division for Science, Innovation & Know-how. April 9, 2024
³Scammers conceal dangerous hyperlinks in QR codes to steal your data, Federal Commerce Fee (Alvaro Puig), December 6, 2023.
Methodology: Snapshot and canopy stat knowledge characterize telemetry from Microsoft Defender for Workplace 365 displaying how a QR code phishing assault was disrupted by picture detection expertise and the way Safety Operations groups can reply to this risk. Platforms like Microsoft Entra supplied anonymized knowledge on risk exercise, resembling malicious electronic mail accounts, phishing emails, and attacker motion inside networks. Further insights are from the 78 trillion every day safety indicators processed by Microsoft every day, together with the cloud, endpoints, the clever edge, and telemetry from Microsoft platforms and providers together with Microsoft Defender. Microsoft categorizes risk actors into 5 key teams: affect operations; teams in growth; and nation-state, financially motivated, and personal sector offensive actors. The brand new risk actors naming taxonomy aligns with the theme of climate.
© 2024 Microsoft Company. All rights reserved. Cyber Indicators is for informational functions solely. MICROSOFT MAKES NO WARRANTIES, EXPRESS, IMPLIED OR STATUTORY, AS TO THE INFORMATION IN THIS DOCUMENT. This doc is supplied “as is.” Data and views expressed on this doc, together with URL and different Web web site references, could change with out discover. You bear the chance of utilizing it. This doc doesn’t offer you any authorized rights to any mental property in any Microsoft product.